Top 4 Ivanti Competitors and Alternatives for 2024

Ivanti Secure VPN is a popular remote access VPN solution used by businesses, organizations and governments worldwide. Unfortunately, five new zero-day vulnerabilities in Ivanti have been discovered this year, which allow an unauthenticated attacker to execute remote code and compromise systems.
French cyberdefense search engine ONYPHE has said that 29,664 Ivanti Secure VPN appliances are connected to the internet. This leaves thousands of devices at risk of being exploited through the newly discovered zero-days.
While Ivanti VPN has released patches to address these zero-days, it may be safer to consider looking for alternative VPN solutions for your organization. Here, we look at the top Ivanti competitors and alternatives for 2024.
Top Ivanti competitors and alternatives: Feature comparison
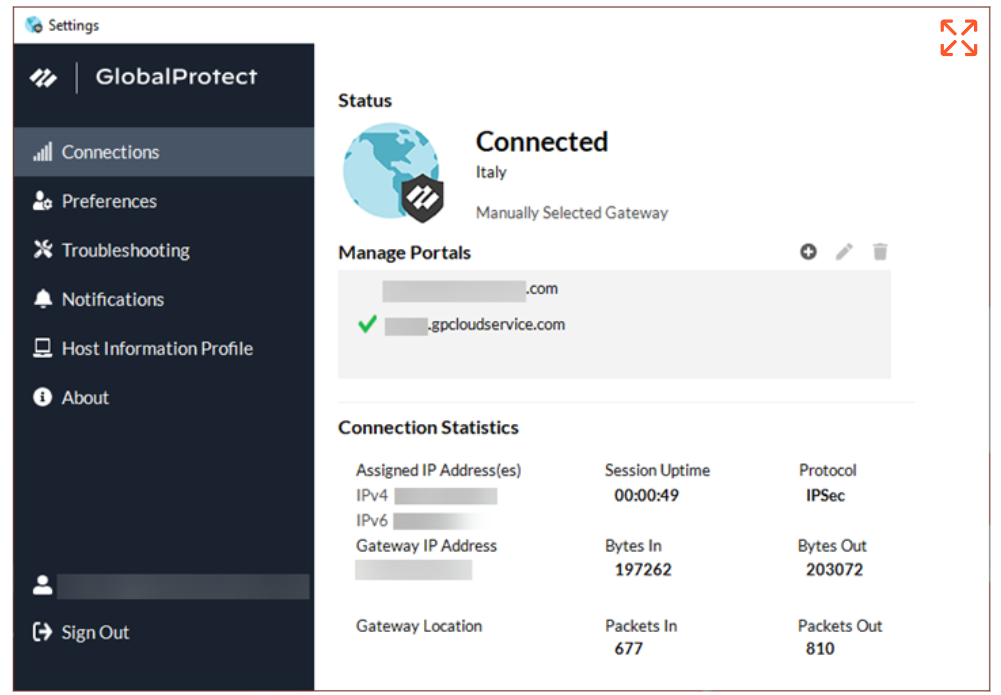
Palo Alto GlobalProtect: Best for ease of use
Palo Alto GlobalProtect is a top option for protecting your hybrid workforce with its high-quality IPsec/SSL VPN connection. It supports an extensive list of multi-factor authentication methods and includes cookie or certificate-based authentication.
GlobalProtect makes it easy for businesses to monitor all aspects of their network. It can detect applications, ports and company-owned or employee-owned devices, eliminating blind spots that could house vulnerabilities or risk areas. It also enables organizations to set precise access policies for company resources, which is crucial for companies with remote workers within various levels and departments.
Why we chose GlobalProtect
GlobalProtect made the list for its seamless set-up process and easy to use interface.
Pricing
- Contact the vendor for pricing information.
Features
- Secure remote access.
- Advanced threat and phishing protection.
- URL filtering against malicious domains.
- Supports MFA.
Pros
- Available free trials and demos.
- Easy to set up and use.
Cons
- Can be difficult to troubleshoot connectivity issues.
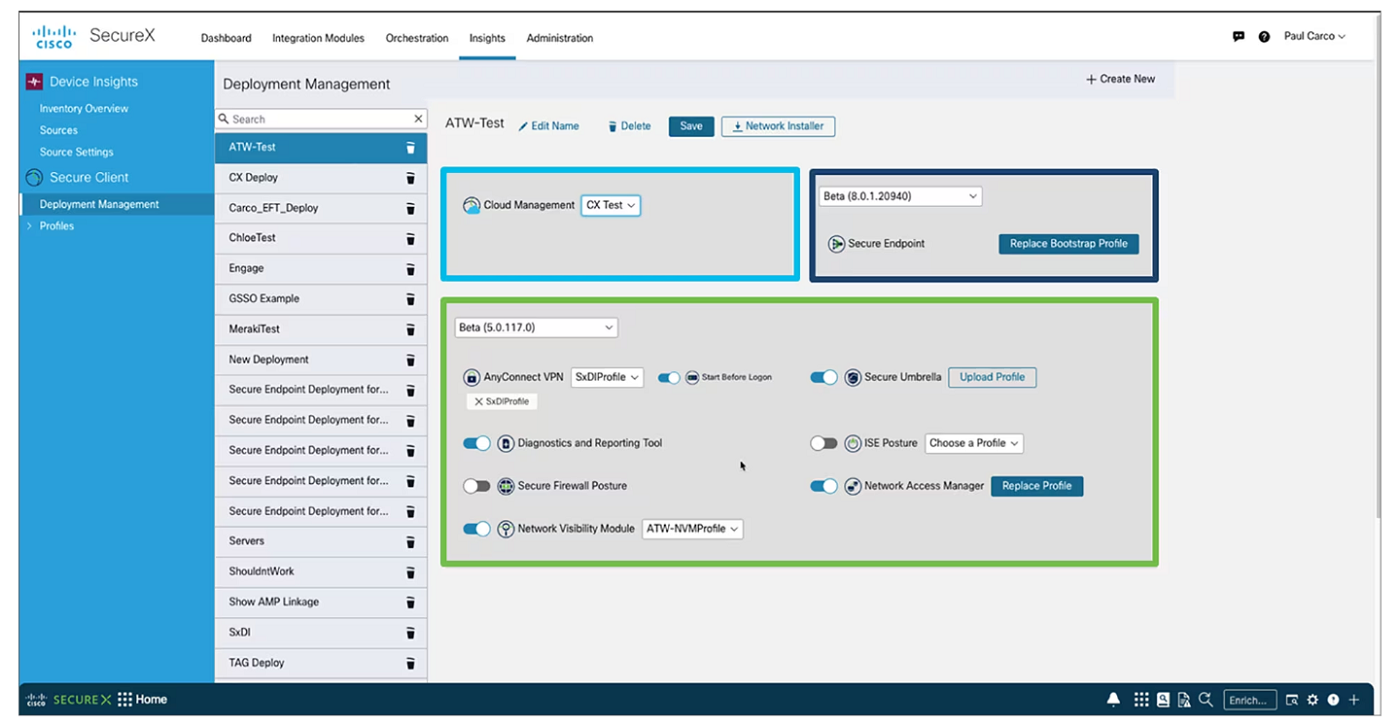
Cisco Secure Client: Best for reliable VPN performance

Cisco Secure Client is a go-to VPN solution for businesses for good reason. Formerly known as Cisco AnyConnect, Secure Client provides remote workers with an easy and secure way to access the enterprise network from anywhere and via multiple devices. Many users have lauded Secure Client’s VPN connection for being fast and reliable — an important aspect for businesses that don’t want network connectivity issues interfering with operations.
Aside from supporting MFA through Cisco Duo, Secure Client can be used with Cisco’s Endpoint Security Analytics to get a broad view of user behavior. In a world of exploited software and hacked remote devices, gaining insights on endpoint behavior is more important than ever.
Why we chose Cisco Secure Client
We chose Cisco Secure Client for its reputation as a reliable and overall stable VPN solution.
Pricing
- Contact the vendor for pricing information.
Features
- Can verify authorized and unauthorized access.
- Provides endpoint visibility and analytics.
- Supports MFA.
- Policy-driven access to corporate resources.
Pros
- High level of security.
- Stable performance and connection.
- Free trial available.
Cons
- Interface looks outdated.
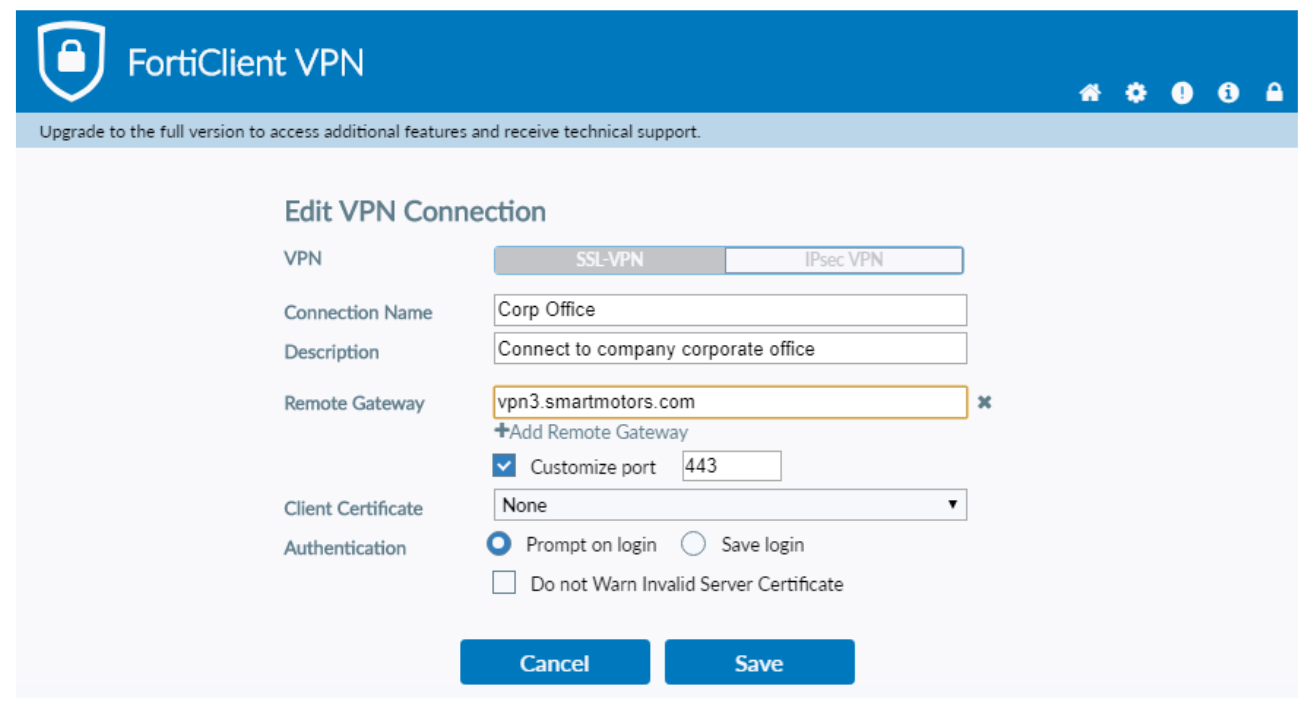
Fortinet FortiClient: Best for supported deployment

Fortinet FortiClient is a lightweight VPN that provides endpoint protection and secure access using zero-trust principles. It utilizes an AI-based antivirus, an application firewall and ransomware protection to provide stronger protection against malware.
Fortinet has split-tunneling functionality, letting users dictate which applications are excluded from the VPN connection. It also offers professional services that can assist businesses with deployment, forensics analysis and configuration.
Why we chose Fortinet FortiClient
We selected Fortinet FortiClient for its impressive customer support and additional deployment and monitoring services.
Pricing
- Contact the vendor for pricing details.
Features
- Automated response against compromised endpoints.
- Zero Trust Agent with MFA.
- Central logging and reporting.
- Split-tunneling.
- SSL and IPsec VPN.
- Offers additional professional services for its software.
Pros
- Affordable.
- Support-guided deployment.
- Customizable authentication.
Cons
- May experience connectivity issues.
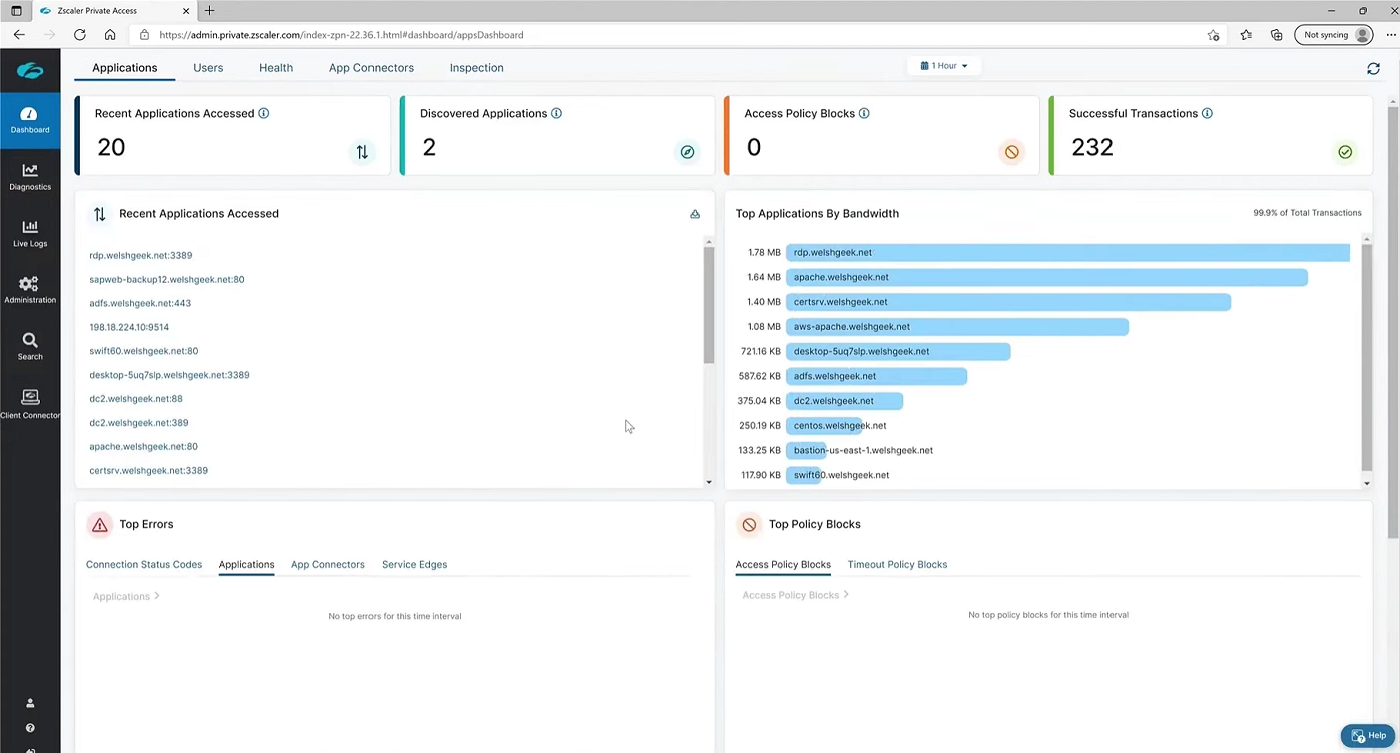
Zscaler Private Access: Best for shifting to zero trust

While not a VPN per se, Zscaler Private Access (ZPA) serves as a strong option for enterprises looking to secure their remote workers. ZPA is a zero trust network access (ZTNA) solution that routes traffic to the cloud and away from traditional data centers, reducing the risk of unauthorized access to company resources.
With ZPA, remote workers can access applications directly from the cloud, not through a remote network. This improves overall performance and restricts hackers from compromising private applications.
Why we chose Zscaler Private Access
Zscaler made this list as a good choice for businesses that want to move away from legacy VPNs and shift toward zero trust solutions.
Pricing
- Contact the vendor for pricing information.
Features
- On-campus ZTNA.
- Cloud-based.
- Risk-based policy engine.
- AI-powered app segmentation.
Pros
- Minimizes risk against zero-day exploits.
- Lower latency for applications.
- Option for software demo.
Cons
Remote access VPN key features
Before choosing a remote access VPN for your business, there are a few features you should consider.
Look at the VPN’s security features
The main priority of remote access VPNs is to secure company resources. With that, make sure that your chosen VPN offers strong security features like high-end encryption and easily configurable access control options. These features ensure company resources are unreadable to malicious hackers and can only be read by those authorized to do so.
Consider logs and visibility capabilities
A feature that Ivanti users should look at specifically is logging and visibility capabilities. As explained in the Ivanti report, VPN device and file logs are two indicators to look at when dealing with a breach. A VPN that provides extensive logging information of all events within a network can be crucial in discovering and verifying suspicious activity.
See how easy it is to deploy
Remote access VPNs require remote workers to install the VPN on their personal devices. With this, it’s important to select a VPN solution that’s easy to deploy and set up. The easier it is to set up, the higher the chance for a business to secure their data. While deployment can vary from user to user, you can check out user reviews of different VPN providers and how easy it is to implement their software.
It’s also beneficial to see if a VPN vendor provides additional services or extended customer support when deploying their VPN.
Check support for multi-factor authentication
Since company resources will be accessible from anywhere in the world, a remote access VPN should have a wide range of MFA options to protect against unauthorized access to these files. While MFA is mostly ubiquitous among all VPN solutions, it’s a crucial component of making sure that only authorized users gain access to sensitive information.
Having multiple MFA options also helps reduce the time needed to log in to a company network, as it provides employees with more ways they can authenticate themselves.
Take pricing in consideration
Even with affordable VPN solutions, costs can rise when a business needs to secure hundreds of remote employees. Consider whether your budget can cover all your workers and the requisite software needed to maximize security.
In addition, take advantage of free trials or demo accounts that let you test drive remote access VPNs before spending on an initial license.
How do I choose the best remote access VPN for my business?
As businesses come in all shapes and sizes, the best remote access VPN will depend on the particular needs of your business. However, fundamental features like ease of deployment, support for MFA and access control configurations are some of the main things to consider when choosing a remote access VPN.
It’s also important to keep up to date with news regarding VPN providers and possible vulnerabilities or involvement in data breaches — such as the unfortunate case with Ivanti Secure VPN.
Methodology
While there are numerous business-centered VPNs, not all VPN services are created equal.
I chose the four solutions above based on their security features, remote access control capabilities, authentication options and customer support. These were done through an extensive review of official product documentation and their corresponding websites.
I supplemented these findings by analyzing user reviews and testimonials from Gartner, TrustRadius and G2 to ensure that real-world performance was properly represented.
I also considered which VPN solutions would fit best for businesses currently using Ivanti Secure VPN and want to switch given the recent vulnerabilities with their software.

